Technology
How Spearphishing Works and How You Can Catch It
Cybercriminals are constantly evolving their methods, and spearphishing is one of the most deceptive tactics in their arsenal.
These attacks can be difficult to spot, as they often appear to come from someone you know and trust, like a colleague or business partner.
What is Spearphishing?
Spearphishing is one of the most targeted forms of phishing attacks. Unlike regular phishing, where attackers send mass emails to random users, spearphishing is highly focused on specific individuals or organizations. These attacks often come disguised as legitimate communication, making them harder to detect.
The goal of a spearphishing attack is to trick the recipient into revealing sensitive information, such as login credentials or financial details, or to execute malicious software by opening a link or file attachment. Attackers invest time in crafting their messages to appear trustworthy, increasing the chance of success.
Key techniques attackers use for spearphishing:
- Email spoofing: Attackers send emails that look like they’re from someone you know by slightly changing the sender’s address.
- Malicious attachments: The email might include a file (like a document or PDF) that contains harmful software when you open it.
- Phishing links: They provide links that seem legitimate but lead to fake websites or downloading malware.
- Social engineering: Attackers learn details about you from social media or other sources to make their messages more convincing.
- Urgent requests: They pressure you to take quick action, like updating your password or paying a bill immediately, so you don’t think it through.
- Credential harvesting: The goal is to get you to enter your login details on a fake site so they can steal your information.
Detecting a Real-World Spearphishing Attack
Because spearphishing attacks are highly targeted, they can be very hard to spot. Even if an email looks like it’s from someone familiar, like a colleague, it might actually be a carefully crafted spearphishing attempt. Just seeing a familiar name in your inbox doesn’t mean the message is legitimate—it could be part of a well-planned attack.
To understand how these attacks work, let’s look at a real-world example. Using a tool like ANY.RUN’s sandbox, which provides a secure, isolated environment, we can safely investigate suspicious emails and attachments without risking harm to our systems.
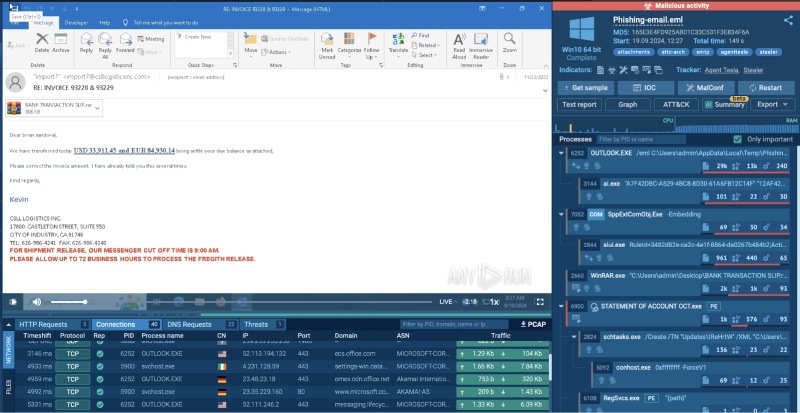
In this example, we received a suspicious email claiming that a payment had been made. The attacker wrote that the recipient had made a mistake in the invoice, asking them to check the attached document and correct the amount.
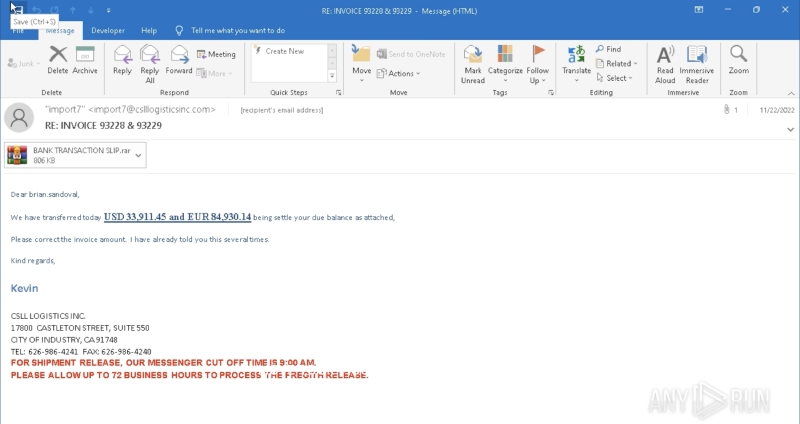
This tactic is designed to create urgency, pushing the recipient to act quickly without double-checking the email’s authenticity.
Using the ANY.RUN sandbox, we download the attached file to see what it really is.
Inside the archive, there’s a file named “STATEMENT OF ACCOUNT”—a tactic cybercriminals use to disguise harmful files with names that sound legitimate. In this case, the file is an executable, which is uncommon for typical business communications.
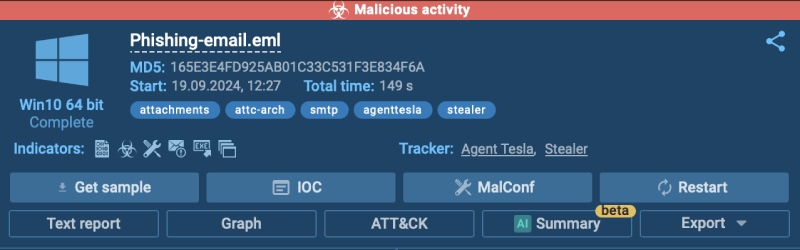
With the sandbox, we can safely open this file and watch what happens. As soon as it’s launched, the sandbox detects malicious activity.
The system confirms that the computer has been infected with Agent Tesla, a type of malware that allows attackers to steal sensitive information and spy on the victim’s activity.
How a Sandbox Can Help Analyze Phishing and Malware
One of the easiest ways to avoid falling victim to spearphishing attacks is to analyze suspicious files, emails, and links in a sandbox environment. A sandbox allows you to safely open and execute potentially dangerous files or URLs without putting your device or data at risk.
Simply upload the suspicious file or copy and paste the URL inside the sandbox and see how safe or dangerous it is to open it on your real computer.
Technology
Naolozut253 Explained: Is This Mysterious Code Really Changing Digital Life?

Unusual codes, words, and terms often appear on our screens while scrolling on the internet. These unknown terms quickly gain everyone’s attention, and out of curiosity, people start associating with a certain meaning, without knowing its context or inquiring. Naolozut253 is one such term, whether it is a software tool, an algorithm, a cybersecurity concept, or simply an internet-generated label? Let’s explore what it means, how it impacts your digital life, and more, so keep reading.
Also Read : TechSlassh.com Explained: How the Blog Blends Technology, Lifestyle, and Everyday Insights
What Is Naolozut253?
As of writing, Naolozut253 is not an official word or name of any product, academic research, or mainstream software documentation. It is not related to:
Established cybersecurity frameworks
Known programming languages
Registered software tools
Official digital protocols
However, Naolozut253 can be related to:
A placeholder or internal project code
A speculative digital concept
A fictional or experimental identifier
A community-created term
This clarification suggests that the popularity of Naolozut253 comes from ambiguity and the mystery around the word’s meaning.
Why Is Naolozut253 Being Called “Mysterious”?
Well! We don’t know the word “Naolozut253 “‘s exact meaning, so here are the possible reasons behind the title of “mysterious”:
Complex Naming: Naolozut253 is an alphanumeric word and resembles encrypted keys or backed system identifiers, which make it sound technical or secretive.
Online Speculation: Online forums and blogs often start discussions on unclear terms without concrete evidence to attract readership.
Association With Technology: Naolozut253 looks like a digital term that is connected with digital transformation, AI, or cybersecurity. This possible association can be the reason behind its mysterious nature.
Is Naolozut253 Changing Digital Life?
If we carefully analyze the available details, we can conclude that:
There is no documented evidence that Naolozut253 powers major systems
It is not listed as a recognized software framework
No verified cybersecurity warnings or innovations reference it
Which means there is no factual confirmation available that it is transforming digital environments.
However, it can be associated with broader trends in digital life, such as:
Increasing reliance on code-based systems
Growing interest in cryptography and identifiers
Curiosity around emerging digital frameworks
How Codes Like Naolozut253 Fit Into Digital Culture
As we know, Naolozut253 is not a recognized term yet, but similar codes to Naolozut253 are used in:
Software development projects
Internal beta versions
Database identifiers
API tokens and encryption strings
In digital culture, it is common to use code like Naolozut253 to represent behind-the-scenes systems that are related to backend users.
Should You Be Concerned?
We don’t want to create unnecessary fear among our readers; there is no evidence regarding Naolozut253.”
A cybersecurity threat
A malware risk
A data privacy issue
However, if you face this code in real life, make sure to:
Verify the source
Avoid downloading unknown files
Check for official documentation
These practices will protect your system from being compromised.
The Psychology Behind Digital Mystique
Naolozut253 has become a fascinating term. This fascination comes from the ambiguity of how digital systems operate. Today, we live in a digital world where most technology operates quietly in the background, so it is common to see unfamiliar labels that are perceived as powerful or secretive.
However, in reality, most alphanumeric codes are either:
Internal development markers
Randomly generated identifiers
Experimental or conceptual labels
The mystery factor comes from interpretation, not reality.
Is Naolozut253 Legit or Fictional?
As we have already mentioned earlier in this article, as of now, there is no formal documentation available regarding Naolozut253 that is widely recognized. Naolozut253 code most likely to be:
A conceptual or experimental name
A fictional or placeholder identifier
A digital term amplified through speculation
Frequently Asked Questions (FAQs)
What Is Naolozut253?
It is an undefined digital term or code and not a verified technology.
Is Naolozut253 A Cybersecurity Threat?
There is no concrete evidence to prove it is harmful.
Is It Linked To AI Or Blockchain?
No data regarding its connection with AI or Blockchain is available right now.
Conclusion
Naolozut253 seems like a digital curiosity rather than an actual software, word, or tool. It is an alphanumeric word that can be anything, as we don’t know its precise meaning as of now, so it is better to avoid discussing it further without knowing its details. In this article, we shared available details about Naolozut253 and discussed its potential meaning in detail. We hope you enjoyed reading this post and found it informative. If so, then do share this post with others as well.
Technology
TechSlassh.com Explained: How the Blog Blends Technology, Lifestyle, and Everyday Insights

Today, we are observing a new trend in the blogging industry, readers' preference is changing, now they want everything in one platform. Readers prefer platforms providing quality information on multiple categories nowadays. This changing trend has inspired many platforms to become general blogging platforms from niche oriented-one.
TechSlassh.com is one such blog that covers multiple categories without focusing on one core category. In this article, we will explore its details, discuss the type of content it publishes, how reliable it seems, and more, so keep reading.
What Is TechSlassh.com?
TechSlassh.com is a general blogging website covering multiple content categories from technology to lifestyle. It doesn’t limit itself to a particular niche and narrows down its content choices; rather, it explores several categories, covering multiple subjects, and decides to attract readers of different tastes and reading requirements.
What Kind of Content Does TechSlassh.com Publish?
Primary content categories of TechSlassh.com are as follows:
- Technology
- Health
- Business
- Education
- Celebrity
- Fashion
- Lifestyle
These are its main content categories. You will find multiple blogs under each one, discussing topics of different interests.
Who Is TechSlassh.com Best Suited For?
TechSlassh.com is ideal for:
- Casual readers interested in tech and lifestyle
- Beginners looking for easy-to-understand explanations
- Users who prefer general awareness over deep technical detail
- Readers who like multi-topic blogs instead of niche sites
Generally, general blogging websites are not for professionals or readers who are looking for in-depth analysis of a topic or industry-level research.
What Makes TechSlassh.com Stand Out?
TechSlassh.com excels in several aspects that make it stand out, such as:
- Covers multiple modern topics in one place
- Simple and readable writing style
- Focus on trending and searchable subjects
- Beginner-friendly explanations
Is TechSlassh.com Legit or Not?
It is not a scam; it is a general blogging website that shares content related to multiple categories, covering several subjects, and attracting a wide range of readers. Here are some signs that prove TechSlassh.com is a legit platform:
- Content-based structure with no forced purchases
- No aggressive pop-ups or misleading redirects
- Articles focused on explanation rather than manipulation
However, while it is not a fraudulent platform, you should keep in mind that:
- It is an information blog, not an official authority
- Claims should still be cross-checked for critical decisions
- Some topics may be generalized rather than deeply researched
Overall, it is a general knowledge and awareness site, not an official or credible platform.
Limitations of TechSlassh.com
Everything is not perfect with TechSlassh.com, it has some limitations as well, such as:
- Articles may not go very deep into complex topics
- Some content may overlap with common online information
- Not all topics are supported by expert-level references
You should treat it as a casual website, not a valid source of information.
How to Use TechSlassh.com Effectively
To get the most value:
- Use it to understand new or trending topics
- Follow up with deeper research when needed
- Compare information with trusted sources
- Treat lifestyle advice as general guidance
By following these tips, you can get the maximum benefit from TechSlassh.com.
Frequently Asked Questions (FAQs)
Is TechSlassh.com A Technology-Only Blog?
No, it is a general blogging website that covers multiple content categories.
Does TechSlassh.com Sell Products Or Services?
It doesn’t directly sell products or services, but may influence your decisions with its articles.
Is TechSlassh.com Suitable For Beginners?
Yes, its content is suitable for beginners, as it is written in an easy-to-understand format.
Conclusion
The trend for general blogging platforms receives mixed responses; sometimes it rises, and sometimes it declines. It generally depends on the search engine guidelines. Generally, niche-specific platforms are preferred for research and educational purposes. General blogging platforms like TechSlassh.com are preferred for casual reading sessions. In this article, we shared multiple details about TechSlassh.com. At the end, we hope that you like reading this post and found it informative. If so, then do share this post with others as well.
Technology
Bill Gates’ Smart City Vision in Arizona: Exploring the Future of Urban Living

Bill Gates is one of the richest and most influential personalities around the world. He is promoting the idea of a smart city, and one of the most discussed examples is the Arizona smart city vision associated with Bill Gates. It is framed to integrate the benefits of advanced technology, sustainability, and data-driven planning. This project has global interest, sparked debates about its implementation and consequences, and how future cities will look.
Also Read : Agenda 2030 Smart Cities Explained: The Global List, Goals, and What It Really Means
If you also find this idea interesting, then this article is for you, as we will discuss the vision for smart cities in Arizona, its core aims, and more, so keep reading.
The Origin of the Arizona Smart City Vision
Bill Gates is not involved at the administrative level; he is actively involved in the investment activities that are linked to a proposed master-planned community in the state of Arizona. The vision focuses on building a city from the ground up, allowing planners to embed technology and sustainability directly into infrastructure rather than using older systems.
Arizona was chosen due to:
Abundant open land
Proximity to major tech and logistics corridors
Favorable climate for renewable energy
Rapid population growth
This project is frequently promoted as an opportunity to test next-generation urban planning at scale.
What Makes This a “Smart City”?
Smart cities focus on green transportation, housing, energy, and governance. It doesn’t treat them as an isolated concern, but instead uses data and technology to bring an integral solution.
Key principles behind the Arizona smart city vision include:
High-speed digital connectivity
Smart transportation and logistics
Sustainable energy use
Data-informed urban planning
Mixed-use residential and commercial zones
The primary goal is long-term living conditions and adaptability.
Sustainability at the Core
Bill Gates’ broader philosophy is to stand on sustainability; it is playing a central role behind the motivation of converting traditional cities into smart ones.
Planned sustainability features often discussed include:
Renewable energy integration (especially solar)
Water-efficient infrastructure suited to Arizona’s climate
Reduced carbon emissions through smart mobility
Compact urban design to limit sprawl
By implementing these changes, we can address several environmental challenges and grow with sustainability.
Smart Transportation and Mobility
Smooth transportation is crucial for the effective functioning of any city, and Arizona’s case is not an exception.
Optimized road networks for autonomous and electric vehicles
Smart logistics hubs to support e-commerce and trade
Reduced congestion through data-driven traffic management
Walkable and mixed-use neighborhoods
This approach highlights the change required in smart cities regarding transportation and how it can be achieved.
Economic and Innovation Potential
Contrary to general belief, a smart city isn’t only about technology; it also includes creating economic opportunities for every resident. The Arizona smart cities project, backed by Bill Gates, can:
Attract technology companies and startups
Create jobs in construction, data, and clean energy
Serve as a testing ground for urban innovation
Strengthen Arizona’s position in the future economy
Economic development is important for the sustainability of any city in terms of living. People need earning opportunities.
Public Concerns and Criticism
However, everything is not as good as it seems; some significant challenges need to be resolved, a few of which are as follows:
Data privacy and surveillance risks
Corporate influence over public life
Affordability and accessibility
Whether benefits will reach average citizens
How This Fits the Global Smart City Movement
Globally, the smart city concept is primarily adopted by Europe, Asia, and the Middle East. Bill Gates’ Arizona-linked project follows similar trends to:
Building smart infrastructure from scratch
Using cities as climate and tech laboratories
Long-term planning instead of reactive growth
The Arizona project is implemented on a notable scale with high ambition to start fresh, rather than refixing the existing one.
What the Future Could Look Like
If the Arizona smart city project becomes successful, it can:
Influence how future cities are designed
Provide data-driven insights into sustainable living
Shape policies around urban technology
Redefine how private investment intersects with public planning
However, these outcomes will only come after careful execution, governance, and working toward inclusivity.
Frequently Asked Questions (FAQs)
Is Bill Gates Personally Building A Smart City In Arizona?
No, he is not personally building a smart city in Arizona, but is involved through investment entities.
Is The Arizona Smart City Already Built?
No, it is a long-term development concept and will require significant time to be completed.
What Is The Main Goal Of The Project?
The primary goal of the project is to create a sustainable, technology-driven urban environment for the city.
Conclusion
Smart city is a trending concept; worldwide governments are planning to convert their busiest cities into smart cities to make urban lifestyles sustainable. In this article, we discussed details of Bill Gates’ imaginative city vision in Arizona. We hope that you like reading this post and find it informative. If so, then do share this post with others as well.
-
 Entertainment2 years ago
Entertainment2 years agoBest Kickass Proxy List 2024 – 100% Working to Unblock to Access
-

 Lifestyle2 years ago
Lifestyle2 years agoBanging The Underdog Incident 2022
-

 Entertainment2 years ago
Entertainment2 years agoTamilRockers Proxy 2025: 20+ Working Links, Mirror Sites & VPN Guide
-

 Entertainment2 years ago
Entertainment2 years agoTamilMV Proxy Sites List 2025 – How to Unblock TamilMV Safely?
-

 Fashion2 years ago
Fashion2 years agoTrendy Midi Dresses for Casual Wear: Hair Care Tips Included!
-
 Entertainment2 years ago
Entertainment2 years agoPirate Bay Proxy List 2025: Access The Pirate Bay Safely
-
 Technology1 year ago
Technology1 year agoSSIS 469 – Detailed Guide to Understand The Features and Benefits
-
 Blog2 years ago
Blog2 years agoCy Kass – Family Detail of Alex Wagner and Sam Kass






